As with any infection or intrusion, ransomware gains access to your systems by disguising itself as something innocuous, like an email attachment or embedded link. One of the biggest reasons ransomware remains at the top of the cyber threat watch list is that it has a very high success rate for hackers. Most ransomware infections are designed to slip past standard network security measures.
Once it finds a way around those measures, a ransomware infection follows a particular set of steps:
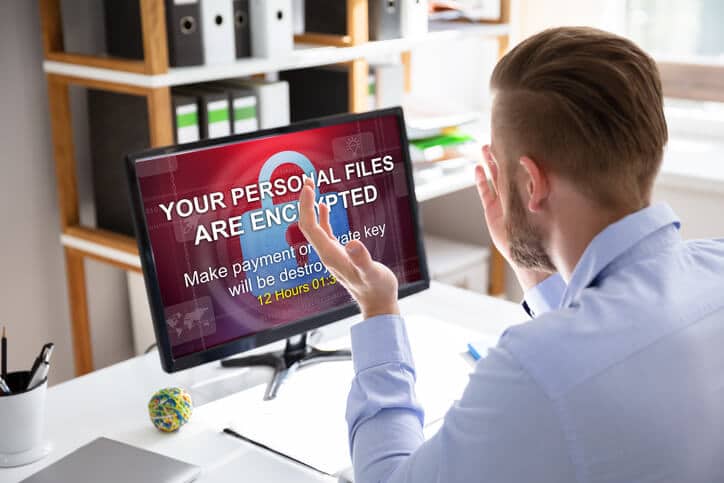
- The virus encrypts all of your business’ valuable and sensitive data, effectively locking you out of your systems
- The hacker responsible will contact you with what amounts to a ransom demand, offering the decryption key in return
- A set amount of time will be given for you to comply – if you don’t, your files will be deleted
If your data backups aren’t reliable and up to date, the only way to get your data back is to pay the demanded fee in exchange for the decryption key, and hope the hacker holds up their end of the bargain. And if your files are in fact returned to you, this is still just the beginning of your problems.
Your network and systems are still compromised. The original infection is still there, and the only way to remove it is to reformat your entire system. If you don’t, nothing is stopping the hacker from re-encrypting your data. The reformatting process can take days, or even weeks depending on the disaster recovery protocols your business has in place. And without data backups to restore from, you may as well have not gotten your files back at all.
End-to-end network security that is thoroughly monitored and maintained can prevent cybercriminals from finding and exploiting weaknesses in your firm’s IT infrastructure. A combination of software, protocols, and regular update and patch management can safeguard your valuable data against loss and theft. But as most of the tactics used to execute a ransomware attack are designed to get past these precautions, training your staff to act as your first line of defense is critical.
Knowing how to spot and avoid spear phishing and social engineering scams can close that gap in your business’ security. Cybercriminals using email to pose as a financial institution, or even a member of your upper management can trick employees into opening infected attachments or links or providing passwords or other sensitive information that allow the hacker to infiltrate your network.
Taking the time to educate your staff can make it significantly more difficult for ransomware to successfully target your business. Reach out to the cyber security experts at {company} to find out more about the resources available to help you protect your business.
Want to learn more about the steps you can take right now to keep your business safe from cybercrime? Contact us at {email} or {phone}. We’re the IT professionals businesses in {city} trust.