Are there potential gaps in your readiness for protracted working from home? This quick-hit business checklist will walk you through the top topics for maintaining productivity and quality with remote workers.
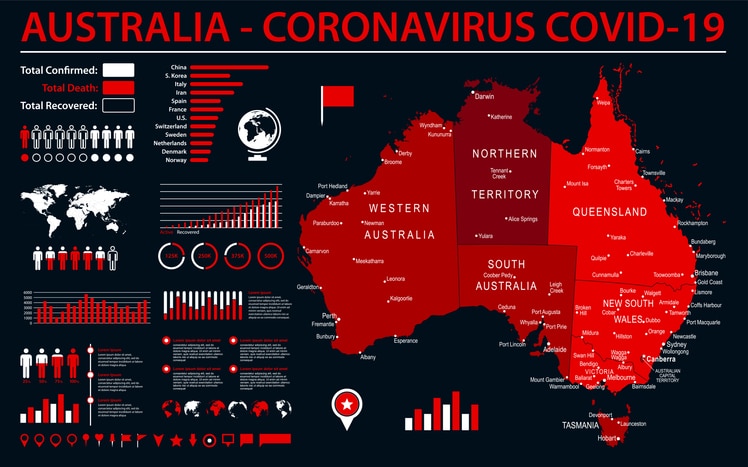
With the onset of COVID-19, there’s been a significant increase in cyberattacks by hackers exploiting the fears of Australians. Scamwatch has reported they’ve received over 140 reports, all related to COVID-19-themed scams and phishing activity. With many people working remotely, networks are being compromised at an alarming rate. Remote workers are vulnerable and easy targets for hackers, making the risks to small and mid-sized businesses more significant than ever.
Data Breaches Are on the Rise
The Office of the Australian Information Commissioner (OAIC) released the Notifiable Data Breaches Report on the 28th of February, 2020. The report highlights the cyberattack statistics from July through December 2019.
- Reportable data breaches rose by 19%
- Malicious attacks increased from 2% to 64%
- The health sector suffered the most targeted breaches, 22% of the total
- The finance sector reported the second-highest data breach rate at 14% overall
- Contact information and identity data was the most frequent form of cyber theft
Since the report was released, the number of COVID-19 related cyberattacks has increased exponentially. Having the right technology and IT provider is more critical than ever to ensure business continuity during the pandemic — and beyond.
Here is your business technology checklist for coronavirus survival.
Move Data Storage to the Cloud
By moving your data to the cloud, you can enjoy greater security and peace of mind. Instead of installing costly hardware and incurring the ongoing maintenance costs associated with onsite storage, storing files in the cloud offers better protection as your vital data is kept safe and is easily accessible by approved users.
Encryption as a service
Encryption ensures that even if data is unlawfully accessed and stolen, it will be completely unreadable and unusable to the thief to protect you, your employees, and business contacts.
Intrusion detection
Monitoring your cloud configuration will detect, prevent, and report potential breaches around-the-clock to keep cybercriminals out.
Virtual Private Network
A Virtual Private Network (VPN) keeps your data safe, especially when using unfamiliar Wi-Fi networks. By investing in and using a VPN, ensure those working remotely are protected because unauthorized third parties can’t get into your cloud-based applications at the same time you’re accessing it.
Check Cloud Application Connections
If your team is already working on cloud software from the office, shifting them to work offsite is simple. If not, you need to migrate to the cloud now. Check security settings to ensure employees can easily log in from a different location. You will also need to provide your team has suitable devices at home to handle the memory and performance needs of your business applications.
Define a Secure VPN Connection Strategy
If workers are logging into your business applications and network from a variety of different home networks, ensure those connections are secure. Put a business VPN in place to encrypt connections for security, and have employees test their connections in advance from home.
Creating a Remote Communications Plan
It’s vital to have a communication policy and plan in place when employees are working remotely. This can include the use of tools like Microsoft Teams and Slack for team communications and using “away” messages and project-based chat channels to keep everyone connected. Team collaboration tools help employees reduce the feeling of being isolated when working remotely.
Check Your Remote IT Support Options
Some organizations have already instituted policies where only staff and emergency personnel can come on-site if needed. This helps prevent the spread of coronavirus, but what happens if you have an IT issue and can’t allow a tech onsite? These issues are handled by having an IT professional log in remotely. Check your options in advance, so you know who to call for remote IT support when you need it.
Use of Video Conferencing
Video conferencing is the next best thing to meeting in person. It can allow you to continue to conduct business with clients as well as keep your employees connected should telecommuting be necessary. Use a reliable conferencing platform and ensure your team has headsets or webcams available, as well as a high-speed internet connection.
The best solution to preventing a cyber incursion is to work with the cybersecurity experts from Steadfast Solutions. The IT professionals at Steadfast Solutions will assess your security needs with fresh eyes and make the recommendations that will help protect your confidential data, maintain business productivity, and conserve your company’s reputation. Call the experts at Steadfast Solutions at 1300-739-335 or email hello@steadfastsolutions.com.au to avoid the potential of lost revenue and serious frustrations for your customers and staff members.